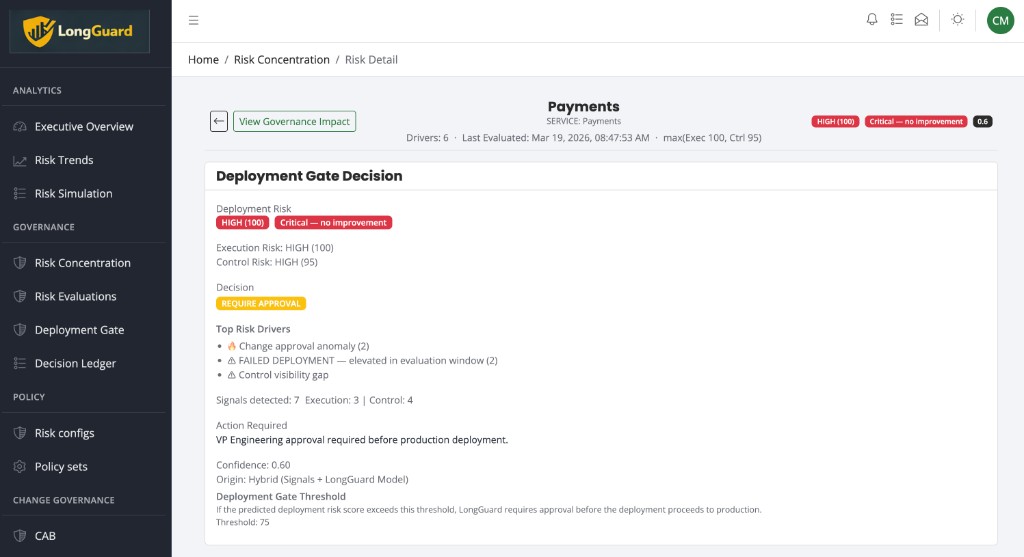
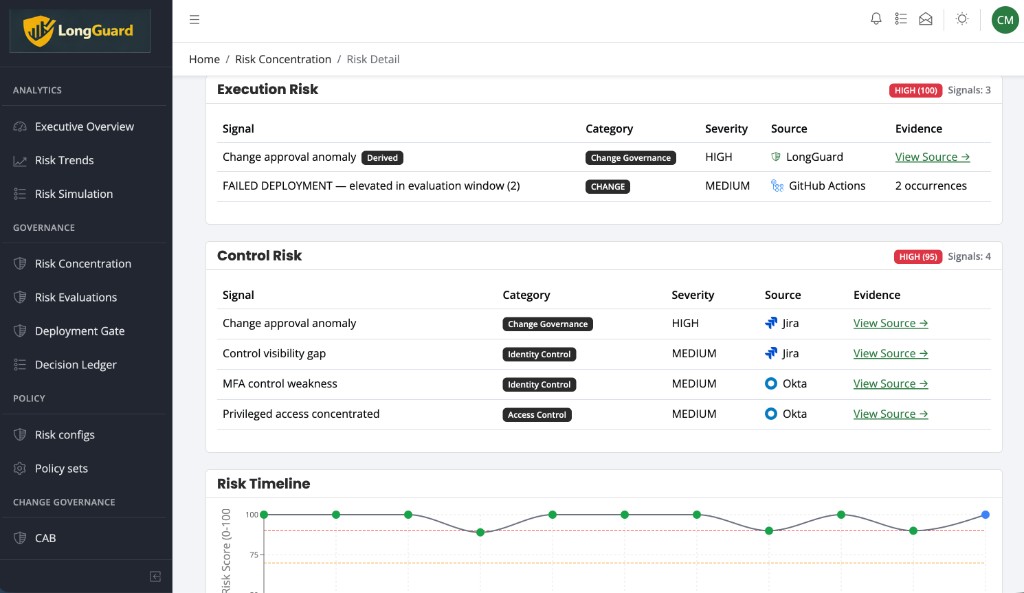
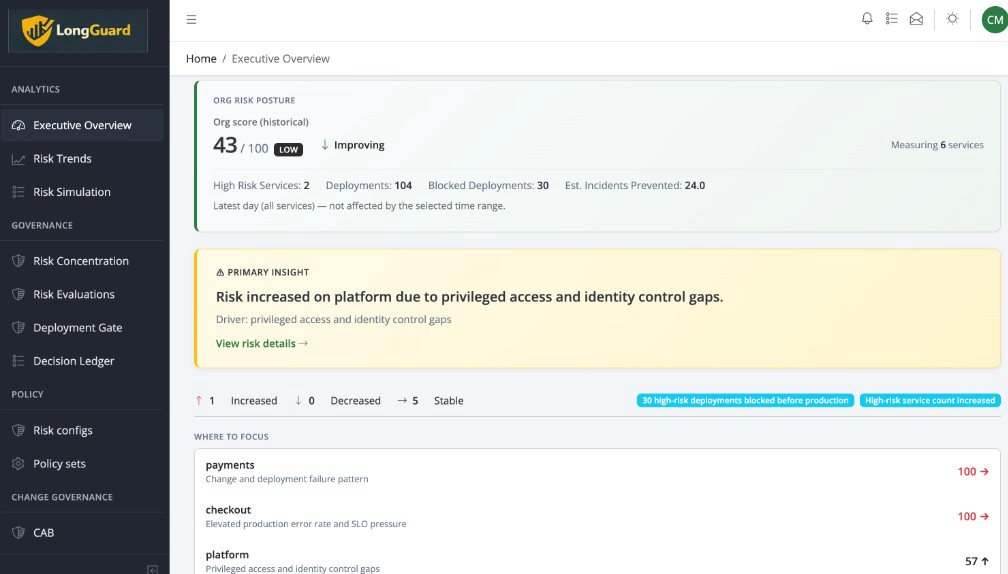
LongGuard evaluates system context, change risk, and approvals to allow, block, or require approval at the moment a deployment is triggered.
All checks passed. Should you still deploy? LongGuard makes that decision before anything reaches production.
LongGuard consolidates outputs from CI/CD, observability, change, and identity systems into one enforceable deployment decision.
Pipelines answer “did the build pass?”, not “is it safe to ship right now?” Without a control point at trigger time, unsafe changes execute and teams learn from outages, not from enforcement.
LongGuard evaluates live system context, change impact, and policy at the deployment control point. The outcome is enforced: allowed to proceed, blocked, or held for approval, not a recommendation buried in a dashboard.
CI/CD answers: Did anything fail?
LongGuard answers: Is it safe to proceed right now?
Even when all checks pass, LongGuard can block deployments based on system state, recent changes, and cross-system policy, at the moment execution is triggered.
Policy and live context determine allow, block, or require approval, not guesswork at the CAB.
Proceed, stop, or escalate, with rationale that approvals can defend.
Enforcement at the control point stops execution when policy or context demands it.
Allow, block, and require-approval outcomes record why, for governance, audit, and post-incident review.
Judge identity and context. Enforce allow, block, or require approval, with a full audit trail.
Fits alongside CI/CD and your toolchain: LongGuard is the control point that decides and enforces whether a change may execute, whether human- or agent-initiated.
Early design partner program open for orgs standardizing policy-driven deployment control.
If you need a single, policy-driven deployment decision before execution instead of another dashboard, we should talk.